Authentication
To access authentication settings, navigate to Administration >> Settings >> Authentication.
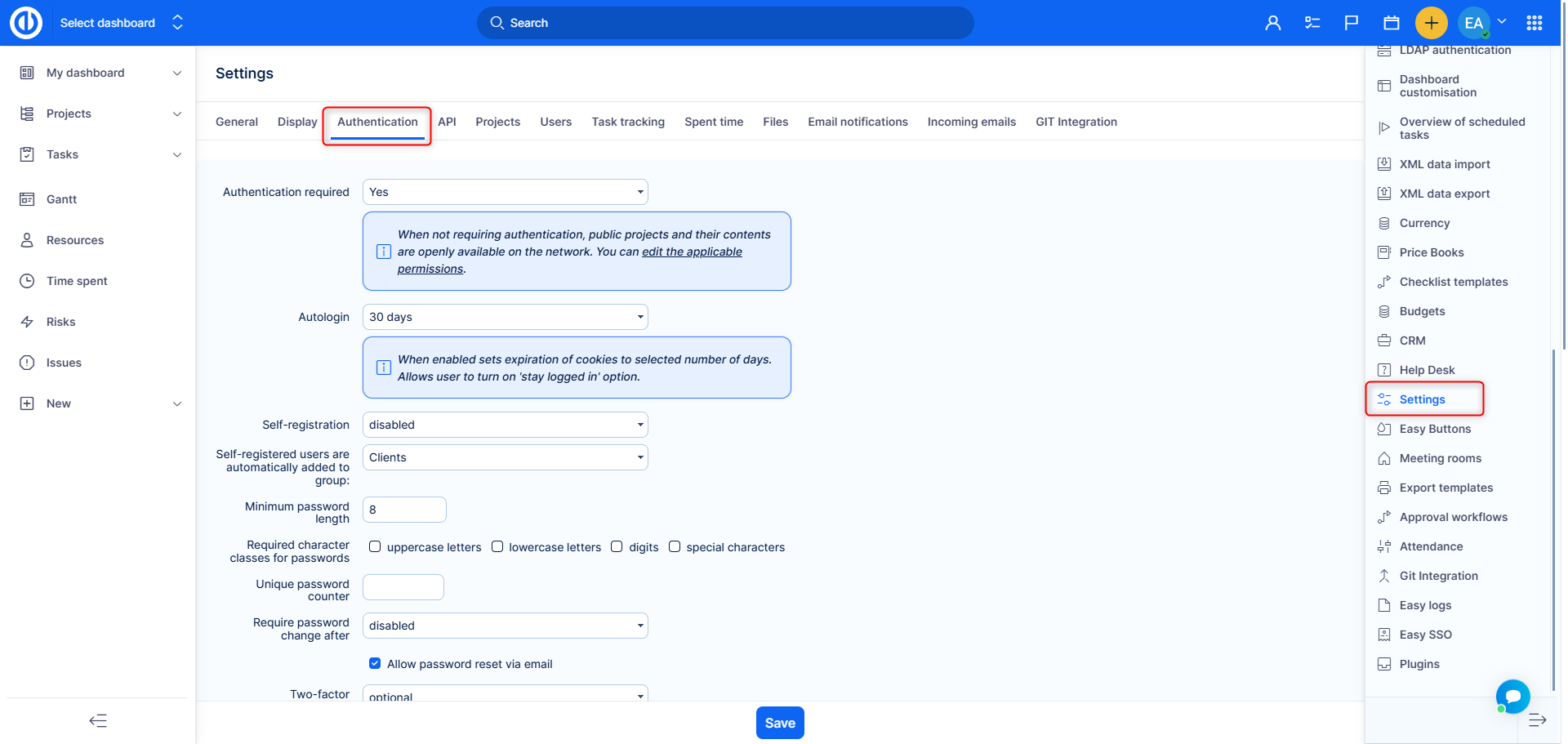
Here you can set up the following options:
- Authentication required – When not requiring authentication, public projects and their contents are openly available on the network. You can edit the applicable permissions for anonymous users in Administration >> Roles and permissions.
- Autologin – How many days is a user logged in using the autologin feature.
- Self-registration – Here you can set if a user can perform self-registration and how to do so.
- account activation by email - An activation link will be sent to the registered e-mail.
- manual account activation - The administrator must activate the user. Registered users can be filtered in the user list by status "registered".
- automatic account activation - The user is activated on the first login.
- Self-registered users are automatically added to group – You can add a self-registered user to an existing group automatically.
- Minimum password length – Enter the requested number of characters.
- To protect your sensitive business data, we strongly advise users not to store their login credentials (login name and password) in their web browsers. If the web browser asks if you want to save the password, don't let it. Otherwise, you expose your user account and all the information accessible from it to a high risk of misuse.
- Unfortunately, there is no application way to prevent saving passwords to the browser. The browsers use all their strength to avoid mechanisms of applications to disallow saving passwords and they do so regardless of the security risk involved.
- Required character classes for passwords – Select uppercase letters, lowercase letters, digits, or special characters. If an entered password does not meet any of these criteria, an error message appears.
- Unique password counter – After how many password changes can a user set up the last password again.
- Required password after – After how many days will the system ask a user to change his password. However, the notifications about password expiration can be turned off on the user profile.
- Allow password reset via email – Check to allow sending the password reset link via e-mail.
- Two-factor authentication – Setting "Disabled" will deactivate and unpair two-factor authentication devices for all users. Setting "Required" will require all users to set up two-factor authentication at their next login. Setting "Required for administrators" will require all administrators to set up two-factor authentication at their next login. Setting "Optional" will let all users enable/disable two-factor authentication on their user profile based on their own decision.
- Two-factor authentication (2FA), often referred to as two-step verification, is a security process in which the users provide two authentication factors to verify they are who they say they are. 2FA can be contrasted with single-factor authentication (SFA), a security process in which the user provides only one factor – typically a password.
- If 2FA authentication is globally active, the user can find the enable/disable option in his user profile so that each user can customize the authentication process at his convenience. No user has the right to activate 2FA authentication for another user. Only the administrator has the right to deactivate it for other users, but he cannot activate it.
- To enable 2FA, you will be asked to scan the displayed QR code or enter the plain text into an authenticator app (e.g. Google Authenticator, Authy, Duo Mobile...). The app is supposed to generate a verification key that you enter back into the respective form in the next step and 2FA is thereby verified and activated.
- Remember devices for X days – Don't ask for a 2FA validation code within the specified number of days if the user's device is already known.
- Validate remembered devices – Check to warn if a user is being logged from an unknown location.
- Session maximum lifetime – How long can someone be logged in before the system automatically logs the user out.
- Session inactivity timeout – How long can someone be inactive before the system automatically logs the user out.
- Unsuccessful login attempts: Enable function – A security feature that automatically blocks the user after submitting an incorrect password multiple times.
- Block user after X attempts – Blocks a user after the specified number of incorrect password submissions.
- When blocked, the user will find the configured notice on the login page. We recommend showing the contact information of the administrator or office who can unblock the user so that they immediately know where to turn to.
- We also recommend enabling the notification for administrators in charge of user management so they can proactively contact the user to find out what happened.
- Manual unblocking – Administrators can easily unblock the user by going to their user profile (do not confuse with user edit form) and clicking "Unblock".
- Block vs lock – This feature is not in any way related to the Lock user functionality, which is used when you want to completely hide the user from the application, for example, if they left the organization. Blocked users are still active, they just can't log in to the application until they are unblocked.
- Display social service icons on the log-in page – Check to display the icons.
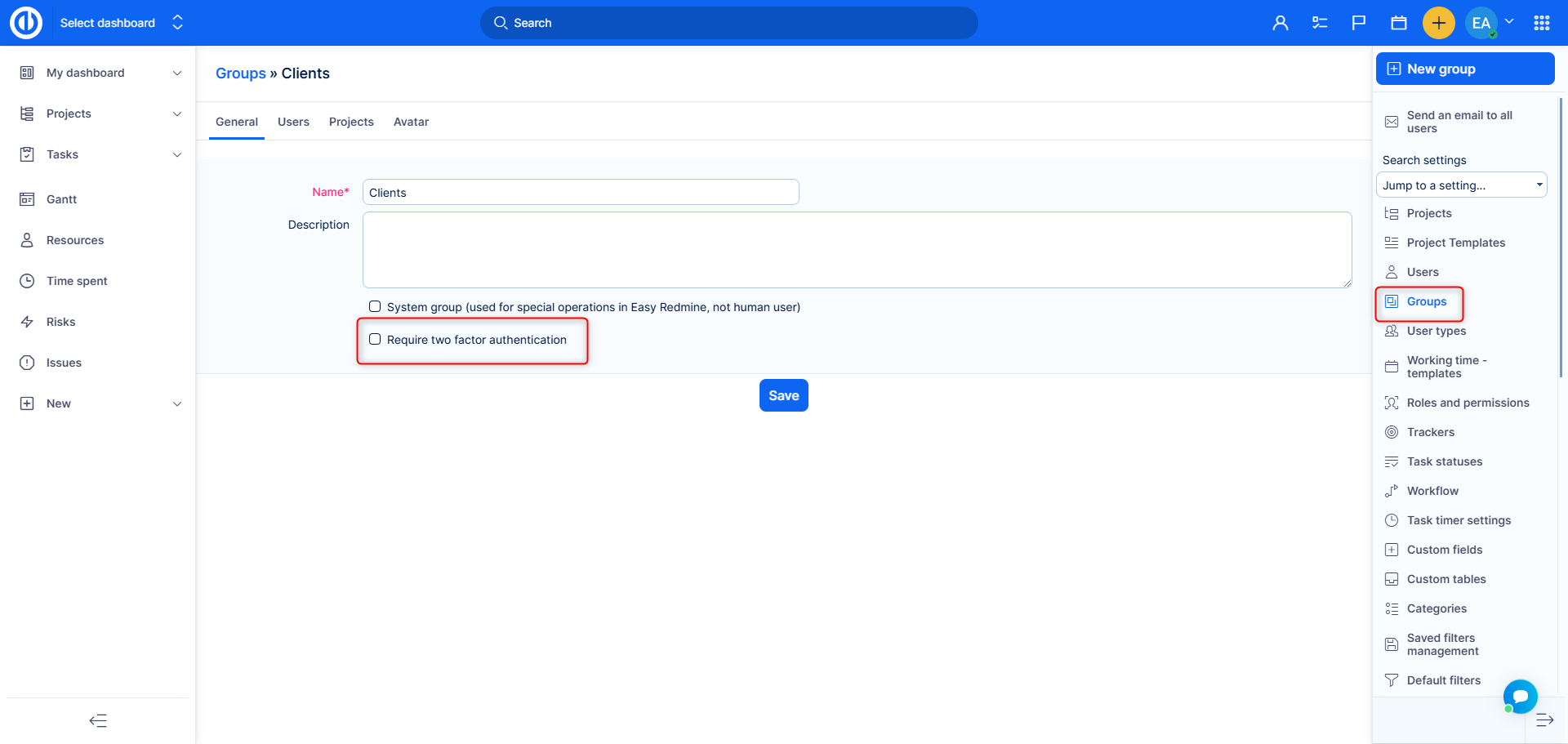
Require two-factor authentication for user groups
It is possible to force two-factor authentication for user groups. If a user is a member of such group (or added into such group), two-factor authentication will be required on his next login. To activate this feature, navigate to Administration >> Groups >> select a group - check "Require two-factor authentication" and save.
Corner situations
- 2FA Verification Fails Due to Time Desynchronization: In rare cases, users may encounter issues when enabling two-factor authentication (2FA) and attempting to verify codes generated by authenticator apps like Google Authenticator or Microsoft Authenticator. Despite the correct setup, the verification may fail.
Cause:
The issue arises when the server’s clock is not synchronized with the Network Time Protocol (NTP). This desynchronization results in a time mismatch between the server and the user's device, causing the time-based one-time passwords (TOTP) generated by the authenticator app to be invalid.
Resolution:
Ensure that the server's clock is synchronized with NTP to match the time on user devices, resolving the discrepancy and allowing successful 2FA verification.